Post quantum encryption
Communication data is protected by 521-bit ECC, double ratcheting and extended triple diffie-Hellman

without rear doors
Ghost does not create international loopholes in its cryptosystems to bypass encryption. no back doors

Brute Force Protection
Enhanced protection of stored data with strong security measures against malicious online and offline brute force attacks

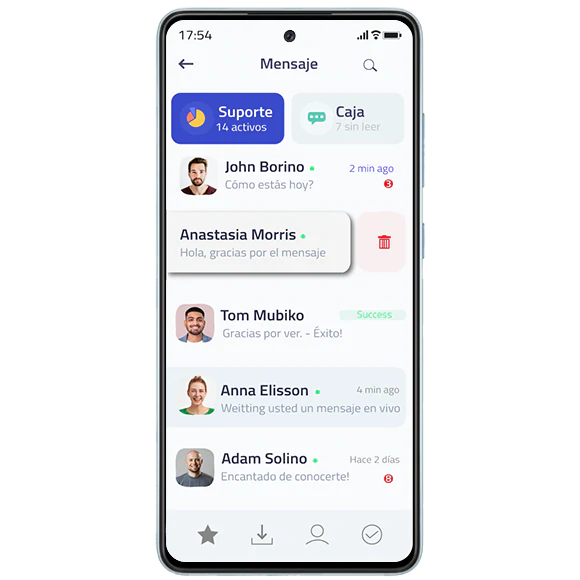
Chat
All messages sent and received from the device are encrypted to ensure private communications.
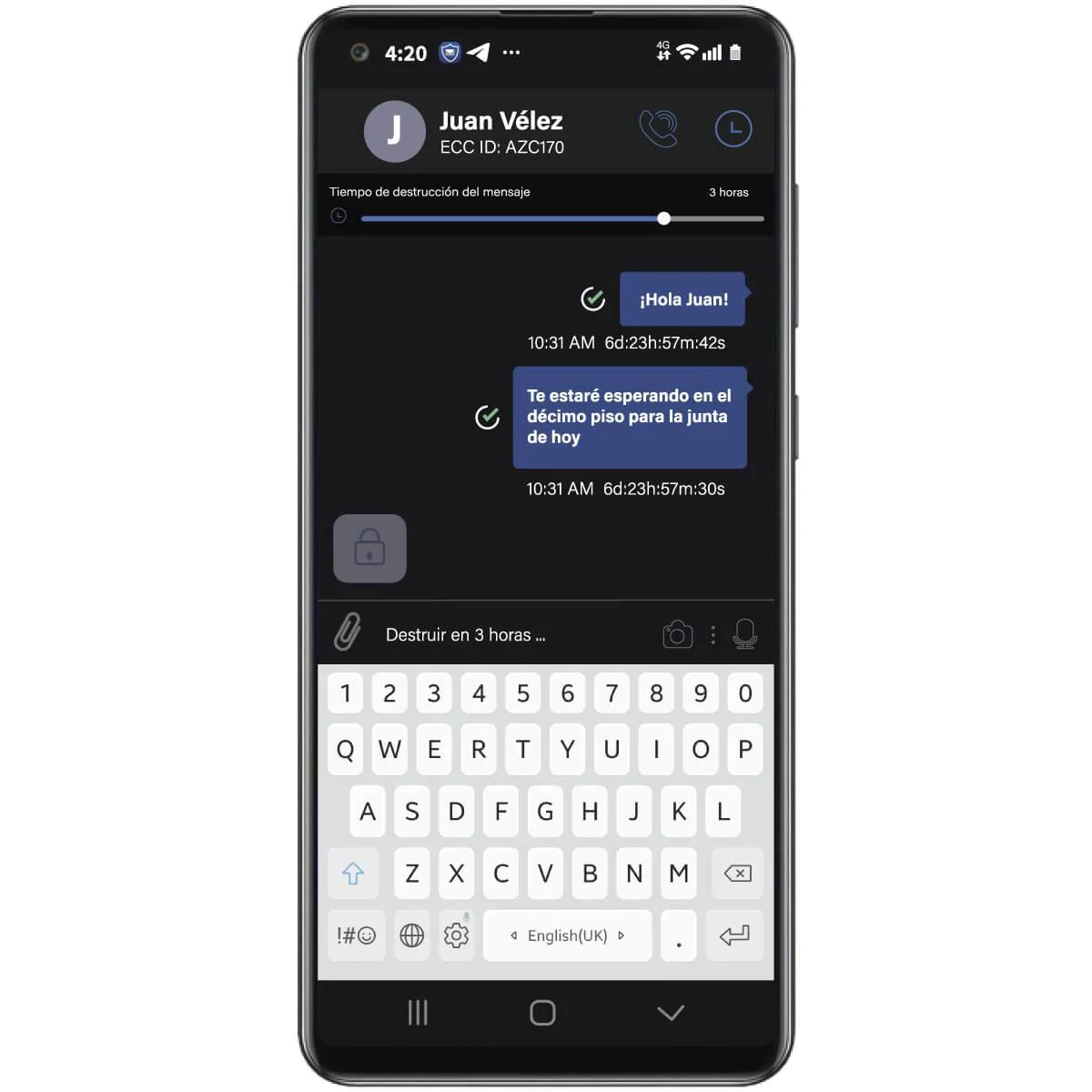
Chat
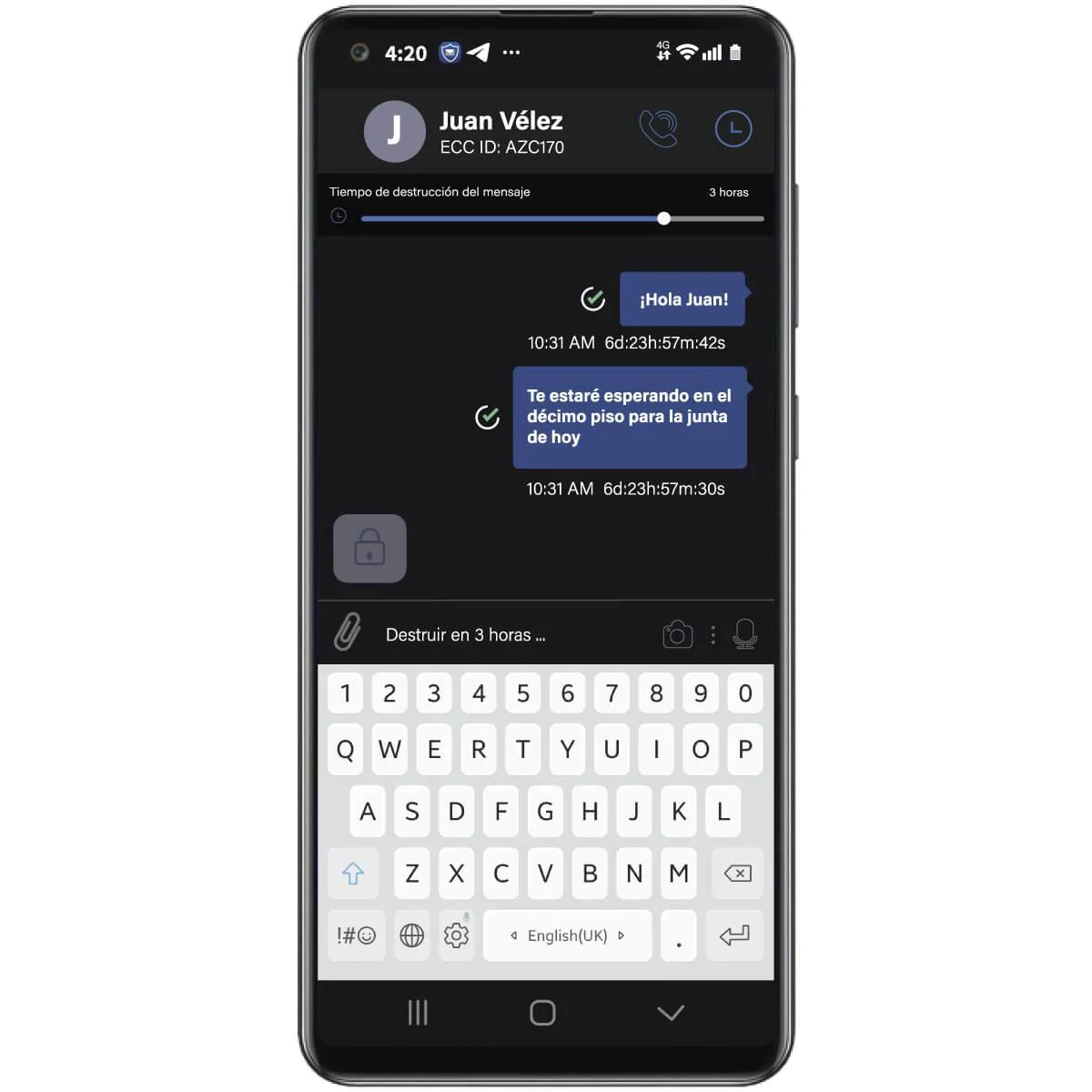
Set messages and emails to be deleted on both the sending and receiving devices after a defined period of time
Chat
Send all multimedia encrypted, including photos, videos and voice notes
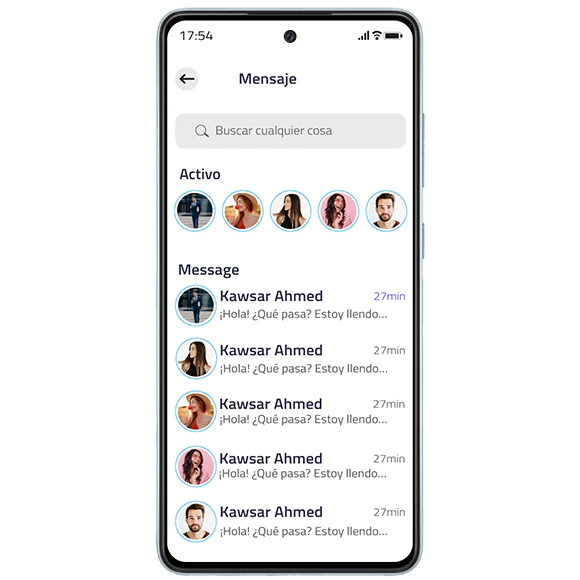
Chat
Ghost uses hybrid encryption with complex mathematical data processing with end-to-end encryption without any chat data being stored on any server
No malicious third party can access the information. With Ghost's military encryption you can be sure that your communications will be protected at the highest level of security.

Self-destructive group chats
Create group chats with a timer. When this expires, the group chat will automatically self-destruct on all members' devices without leaving any traces.

Anonymous group chats
Create group chats with full features in anonymous name privacy to protect the identity of the participants.

Secure all communication
Communication is encrypted and protected from user to user and is transmitted through our decentralized network. All data stored on devices is protected and encrypted

CALLS AND VIDEO CALLS
Real-time voice encryption
Secure and private end-to-end encrypted voice calls that cannot be eavesdropped on by us or third parties.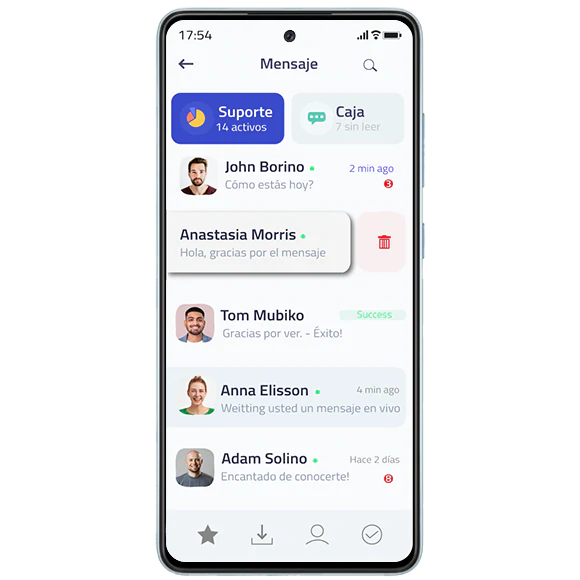
Chat
Set messages and emails to be deleted on both the sending and receiving devices after a defined period of time
Chat
Send all multimedia encrypted, including photos, videos and voice notes
Chat
Ghost uses hybrid encryption with complex mathematical data processing with end-to-end encryption without any chat data being stored on any server
No malicious third party can access the information. With Ghost's military encryption you can be sure that your communications will be protected at the highest level of security.

Panic password
With Ghost you can create a panic password that when entered, immediately deletes all information and messages from the device.

Remote wipe and anti-theft protection
If your device is lost or stolen, you can perform a remote wipe to remove all data regardless of whether or not it's connected to the internet.

External applications
Ghost allows you to install apps from third parties to make communications more versatile
Learn to protect your cell phone and trust Ghost

Encrypted
SIM Card
Protect yourself from cybercriminals and
keep safe your personal information!

E-SIM
Encrypted
Plans
Data or minutes

Encrypted
SIM Card

E-SIM
Encrypted
-
Plans
Data or minutes

Protect yourself from cybercriminals and
keep safe your personal information!
Frequent questions
The panic password feature allows you to set a code to use in case of duress. This will silently erase all the data inside the phone.
In addition to the security and privacy offered by an encrypted cell phone, there will be features such as encrypted chats, remote deletion, encrypted mail, timed messages, cloud storage and multiple encrypted applications.
A remote wipe of the phone can be performed by contacting the provider, this in case the cell phone has been stolen, lost or seized.